https://supportforums.cisco.com/discussion/12326341/sslv3-poodle-vulnerability
http://www.zdnet.com/google-reveals-major-flaw-in-outdated-but-widely-used-ssl-protocol-7000034677/
This is a client security hole. This is a vulnerability in the old SSLv3 (relaying in 80's code), but even if you have all set for using TLS, in many applications the server can trick you to downgrade to SSL and then it can stole you some security cookies.
This vulnerability is a risk in public wifi but not at home or work.
Mozilla says that it is making Firefox 34 safe from POODLE by disabling SSL 3.0 by default. The code which does this is already baked into the Nightly channel, and will make its way to the Aurora and Beta channels also "in the next few weeks".
----------
MicroSoft Advisory and Workarounds:
https://technet.microsoft.com/en-us/library/security/3009008.aspx
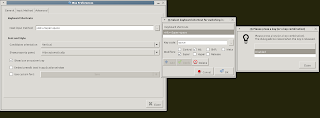
This workaround involves Group Policy Editor. For those using versions of Windows that don't include GPE simply go to Control Panel/Internet Options/Advanced/Security and uncheck the box for SSL 3.0 (SSL 2.0 should already be unchecked).